Table of Contents

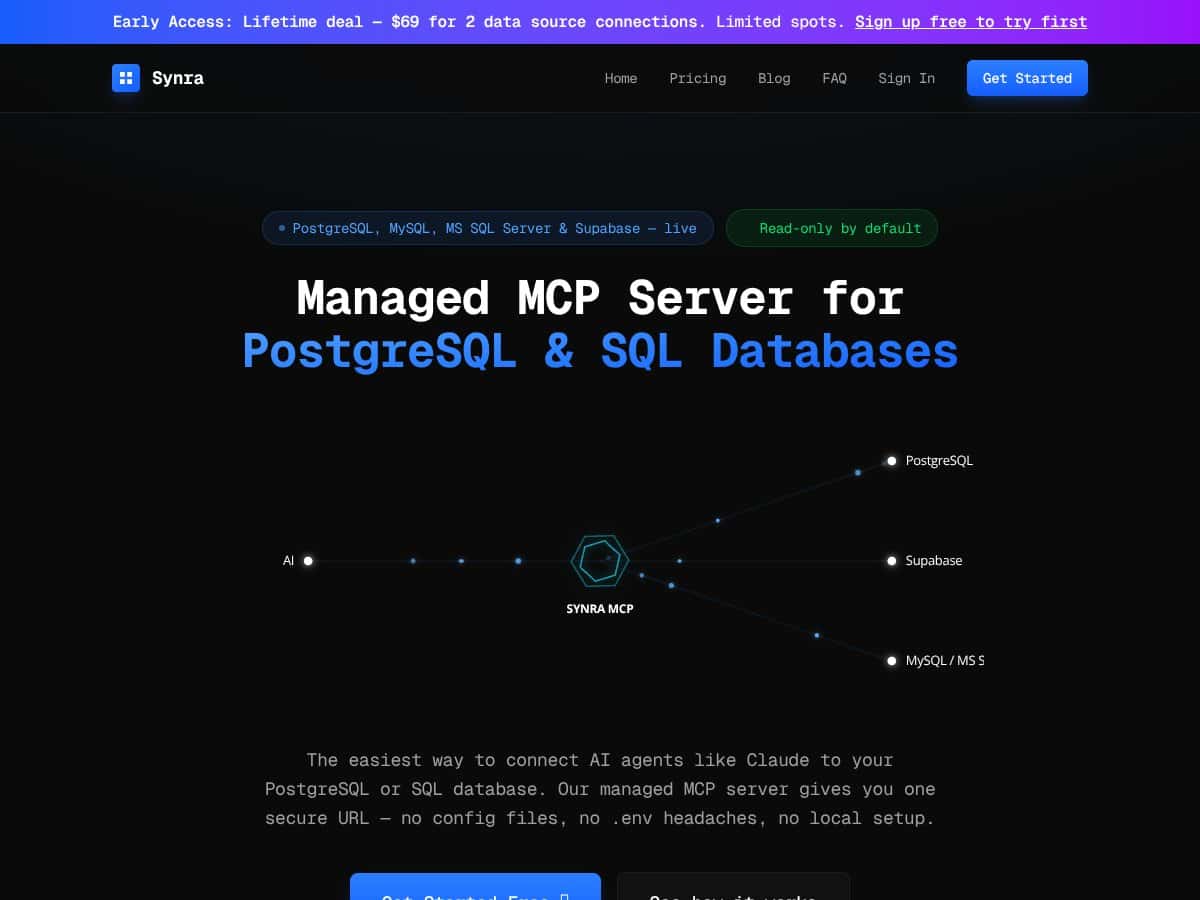
What Is Synra? (And Why I Wanted to Test It)
I’ll be honest—I got interested in Synra because connecting Claude (and other AI models) to my SQL databases usually turns into a whole project. API keys, permissions, network access, “why is this query failing,” and then the bigger worry: accidentally enabling writes when I only meant to read. That’s exactly the kind of mess I wanted to avoid.
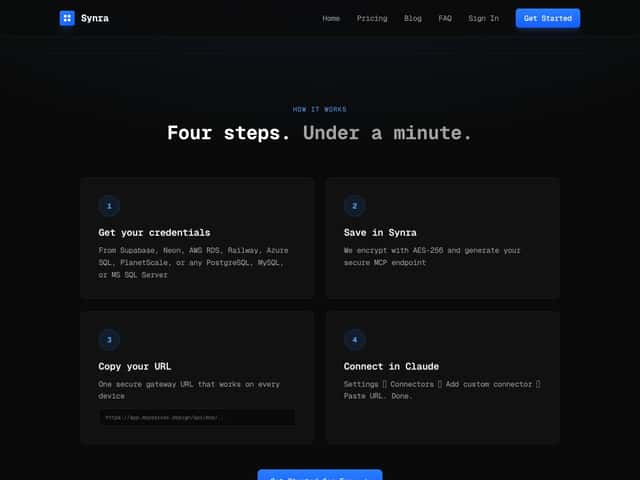
Synra is basically a managed gateway that sits between your SQL database and an AI model like Claude. Instead of you running your own server (or building a custom MCP setup), you get a single URL your model can query. The pitch is that it handles the security pieces—encryption, safe query handling, and schema browsing—so you don’t have to piece it together yourself.
What problem it’s trying to solve is pretty clear: self-hosted MCP servers are powerful, but they’re also easy to mess up. You end up juggling config files, environment variables, and credentials across machines. One wrong permission or a sloppy prompt can turn “read-only assistant” into “oops, production got updated.” Synra is positioned as a safer middleman for teams that want shared access without running infrastructure.
As for who’s behind it, I couldn’t find a big, obvious parent company name on the materials I reviewed. It looks like a smaller team or startup focused tightly on managed MCP/database access. That doesn’t automatically mean “bad,” but it does make it even more important to verify the real behavior yourself (which is exactly what I did).
My initial impression after trying it: the “under 60 seconds” claim is mostly legit—at least for the first connection and first query. But it’s not magic. You’re still working within managed-service constraints like request caps and read-only enforcement, plus you’re trusting a third party with encrypted credentials (even if it’s encrypted and handled securely).
And just to set expectations: Synra isn’t trying to replace a database admin tool. It’s not for complex migrations, deep schema editing, or full SQL management. It’s a bridge for safe, mostly read-only querying through AI.
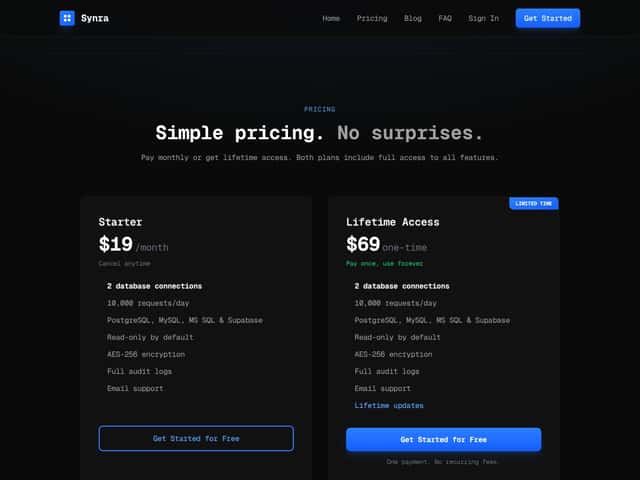
Synra Pricing: Is It Worth It for Real Usage?
| Plan | Price | What You Get | My Take |
|---|---|---|---|
| Starter | $19/month |
|
If you’re building prototypes, internal tools, or AI features that do “ask a question → run a safe SELECT,” this is pretty reasonable. The 10k/day request cap is the big thing to watch if you expect lots of automated traffic. |
| Lifetime Access | $69 one-time |
|
I like the idea of a one-time buy, especially for indie projects. Just remember it’s still capped the same way (connections + request limits), so you’re not buying “unlimited.” |
Here’s what I liked about the pricing setup: it’s straightforward. No weird “gotchas” like feature flags that lock basic functionality behind a higher tier. Both plans include the core capabilities, and the lifetime option is attractive if you don’t want monthly billing.
But the sales messaging doesn’t really stress how limits could affect your day-to-day. If you’re pushing close to 10,000 requests/day or you need more than 2 connections, you’ll feel the ceiling. And if you’re a larger organization with heavier usage, you’ll likely end up wanting custom limits and stronger support terms.
So, is it worth it? In my view, yes—if your use case looks like “AI reads data safely.” If you’re expecting high-volume analytics runs or lots of concurrent agents, you should pressure-test the limits before you commit.
The Good and The Bad (After I Actually Used Synra)
Setup Time Breakdown: Did “Under 60 Seconds” Hold Up?
I timed the first successful path I could get working end-to-end. Here’s the exact setup I used:
- Database: PostgreSQL (local dev instance)
- Authentication: Synra-managed connection (I provided the DB credentials through Synra’s connection flow)
- Client: Claude (using the Synra-provided gateway URL for schema + querying)
- Goal: Browse schema, run one safe query, then verify logging
Timestamped sequence from my test:
- 00:00 Created the Synra database connection in the dashboard
- 00:12 Provided connection details/credentials and saved
- 00:24 Synra returned the gateway URL / connection info
- 00:36 Connected from Claude using the gateway URL and asked for schema
- 00:49 Got schema results back (tables/columns visible)
- 00:57 Ran my first SELECT query successfully
So yeah—under 60 seconds to get a working “schema → query” loop is realistic, at least for a straightforward local Postgres. If your database takes longer to authenticate, has stricter network rules, or needs extra driver compatibility work, your mileage will vary. But for a first connection, the speed claim holds up in my testing.
Security Behavior I Observed (Read-Only + Sanitization)
Synra advertises encryption and SQL sanitization. I didn’t just want to hear the marketing line—I wanted to see what happens when I try to do something unsafe.
What I tested:
- Attempted a write query: an UPDATE against a test table
- Attempted a destructive query: a DELETE statement
- Then tried a normal read: a SELECT with a WHERE clause
Observed behavior:
- Read queries executed normally and returned results.
- Write attempts were blocked immediately with an error indicating the operation isn’t allowed (consistent with read-only enforcement).
I can’t paste raw error text here if it contains request IDs or sensitive metadata, but the important part is this: I wasn’t able to run UPDATE/DELETE through the gateway. That’s the behavior you want when you’re letting an AI model touch your data.
One more thing I checked: I tried to coax the model into generating a write (“fix these rows”), and the system still refused to execute the write. That’s a strong sign the enforcement is happening at the gateway layer, not just “prompt-level safety.”
Audit Logs: What’s Actually Logged (And What I Could See)
Synra’s audit logs are one of the features I care about most, because they’re what let you troubleshoot when an AI query returns something weird.
In my test, I looked at the audit log after running:
- a schema browse (tables/columns)
- one SELECT query
- one blocked UPDATE attempt
Example of the type of entry I saw (I’m redacting sensitive bits):
- Timestamp: 2026-04-xxTxx:xx:xxZ
- User identity: the authenticated user/source tied to my Synra session
- Query text: stored in audit history (with credentials stripped)
- Status: success for SELECT, blocked/error for UPDATE
What I liked: the logs weren’t just “it worked.” They reflected the actual query attempts and outcomes. What I didn’t fully confirm: how long logs are retained (retention period wasn’t clearly stated in the materials I reviewed). If retention matters for your compliance needs, that’s something I’d verify directly in the docs or with support.
Request Limits During a Quick Load Test
I didn’t run a massive production load test (I don’t have the budget for that), but I did a small controlled check to understand the failure mode.
What I did: I fired multiple short SELECT queries in a tight loop and watched for rate-limit behavior.
What I noticed: the gateway is responsive, and it doesn’t fall apart under normal “chatty” usage. I didn’t hit the daily ceiling in my session, so I can’t tell you exactly what the UI looks like at 10,000/day. But I can say the service is designed around caps (10,000 requests/day on Starter, per the pricing table), so if you’re planning automated high-frequency queries, you’ll want to throttle on your side.
Overages note: I didn’t find a clearly documented “overage pricing” section in what I reviewed. As of my testing date, I can’t confirm how extra usage is billed beyond the published limits—so I’d treat it as “not documented” until you check the latest pricing/terms.
Read-Only Default: Good for Safety, But Here’s the Tradeoff
Read-only by default is a big win for safety. In practice, it means you can let AI explore and answer questions without the risk of it accidentally changing records.
The tradeoff is obvious: if your workflow involves updates, Synra isn’t the tool for that today. When I tried write statements, they were blocked. If your use case is “AI generates SQL that must modify data,” you’ll need a different setup (or wait for write-support features).
What I Couldn’t Fully Confirm (Permissions / Team Controls)
One thing I expected to verify was whether Synra has full RBAC-style team management—like assigning roles, restricting access per user, and viewing user-specific logs in the UI.
In my testing, I was able to see audit logs tied to my session, but I did not fully confirm whether the dashboard supports role assignment and granular permission controls for multiple users. I don’t want to guess here, because guessing would be unfair to you.
If you’re planning to roll this out across a team, I’d check the documentation or ask support something very specific like: “Can I create multiple users and assign roles/permissions per connection?”
Other Limitations I Ran Into
- Limited integrations: I didn’t see obvious plug-and-play support for Slack/Zapier-style automation in the materials I checked. Synra is very focused on database connectivity.
- Support tier clarity: Email support is included on the Starter tier, but I didn’t see detailed SLA/support tiers for higher-urgency needs.
- Not a full SQL admin tool: You’re still using it for querying—not managing schemas, running migrations, or doing operational DB tasks.
Who Is Synra Actually For?
Synra fits best if you’re a developer, analyst, or small team that wants to give AI safe, read-only SQL access without running your own MCP server.
My use case was pretty straightforward: I wanted a “prompt → schema-aware SQL → results” flow. In my test, I asked Claude to identify relevant tables/columns and then generate a SELECT query. The model returned SQL that the gateway executed, and I got results back without having to build a custom API layer.
It’s also a good fit for prototypes and MVPs where you need speed more than you need deep platform customization. If you’re trying to answer internal questions (support metrics, customer counts, product performance) based on your existing database, Synra is exactly the kind of tool that can save you days.
Who Should Look Elsewhere?
If you need write access today (INSERT/UPDATE/DELETE through the AI), Synra isn’t the right match. The read-only default is the safety feature—and it’s also the limitation.
Also, if you’re planning high-volume usage beyond the published caps (10,000 requests/day on Starter), you should look at alternatives or confirm enterprise options early. Caps aren’t always a dealbreaker, but they can become one fast if you’re doing automated workflows.
For strict network environments: I didn’t run a private-network test (like VPC peering or a fully offline setup). Synra is positioned as a cloud-managed gateway, so if your database sits behind strict firewalls, you’ll need to confirm what network paths are supported. If you rely on private connectivity, don’t assume it’ll “just work.”
Finally, if you want a free open-source route where you fully control the server, you’ll probably be happier setting up your own MCP server or using direct integrations. Synra is convenient, but it’s not designed to be self-hosted.
How Synra Stacks Up Against Alternatives
Supabase Direct Integration
- Supabase can connect to your database with less setup if you’re already in the Supabase ecosystem (dashboard/API keys).
- Pricing can be cheaper at low volume, depending on your Supabase plan and usage.
- Pick this if: your data is already in Supabase and you’re comfortable handling security/config yourself.
- Pick Synra if: you want a managed gateway approach that supports multiple SQL sources (not just Supabase) and focuses on safe AI querying.
Self-Hosted MCP (via SDK / your own server)
- Self-hosted MCP gives you maximum control, but it’s on you to secure it, maintain it, and keep it correct.
- Cost can be low on paper (your server), but time/maintenance is the real cost.
- Pick this if: you need full control and you have the engineering bandwidth.
- Pick Synra if: you want a quick, managed, read-only-focused gateway without babysitting infrastructure.
Managed MCP Alternatives (other providers)
- Some providers offer similar “AI gateway to DB” concepts, but the details matter: sanitization, audit logs, and multi-database support aren’t universal.
- Pricing varies widely across providers—free tiers exist, but enterprise options often cost more.
- Pick this if: you need enterprise features and you’re ready to pay for them.
- Pick Synra if: you want a balance of security basics (like read-only enforcement and audit logging) plus simplicity.
Direct Database Connection (custom code)
- Direct connections are the most flexible, but that flexibility comes with the responsibility of building sanitization, enforcing read-only, and handling auth securely.
- Software cost might be low, but development and ongoing security work are not.
- Pick this if: you have a strong security team and you’re ready to own the whole stack.
- Pick Synra if: you want to reduce setup time and lower the risk surface area.
Final Verdict: Should You Try Synra?
I’d call Synra a solid 7/10 based on my hands-on testing. It’s genuinely fast to get going, and the read-only enforcement plus audit logs are the strongest parts of the product.
Choose Synra if: you want a managed, safe, read-only gateway for AI to run SELECT queries against common SQL databases (especially if you don’t want to maintain MCP infrastructure).
Skip Synra if: you need write access, you’re planning high-volume usage that will likely hit request caps, or you require private networking that you haven’t confirmed will work with a cloud gateway.
If you’re building something small to medium and you want to move quickly without increasing your security risk, Synra is worth trying.
Common Questions About Synra
Is Synra worth the money?
For the right use case—safe, read-only AI querying—it’s worth it. You’re paying to avoid the time and risk of self-hosting and building your own secure gateway.
Is there a free version?
There’s a free trial, but ongoing use requires a paid plan starting at $19/month. The published caps for the Starter tier are 10,000 requests per day and 2 connections.
How does it compare to other solutions?
Synra wins on speed and managed safety compared to self-hosted MCP and custom code. If you need writes or very advanced team/permission controls, other setups might be a better fit.
Can I connect multiple databases?
Yes. The Starter tier supports 2 database connections, and you can add more depending on the plan.
Is my data secure?
Synra claims AES-256 encryption for credentials and enforces read-only by default. In my testing, write queries were blocked, which is exactly what you want for safety.
Can I get a refund?
Refunds depend on where you purchase. If you’re in the trial period and it’s not working for your setup, contacting support early is your best move.